
PTaaS - Penetration Testing as a Service
Penetration Testing as a Service (PTaaS) represents the evolution of traditional penetration testing, shifting from a one-time event to a continuous, integrated security practice. This modern approach ensures that businesses remain secure throughout the year, rather than just at a single point in time.


How Would Your Business
Benefit
From PTaaS?

Find & Fix
Misconfigurations & Vulnerabilities

Distribute
Remediation
Steps

Manage
The Testing
Process

Reduce
Your Window of
Risk
PTaaS Couldn't be What it is Without Our Dedicated Consultants
At Pentest People, we understand that effective penetration testing is more than just a technical task—it's a journey that requires expertise, guidance, and ongoing support. Our dedicated consultants are here to ensure that every step of your penetration testing experience is seamless and productive.
We believe that the strength of our service lies in the dedication and expertise of our consultants. Their commitment to excellence and customer satisfaction ensures that your penetration testing experience is not only effective but also effortless. With our team by your side, you can trust that your organisation's security is in capable hands.
Here’s how our people-centric approach makes a difference:
What IT teams need is a system that finds vulnerabilities faster, and allows them to distribute, manage and monitor remediation tasks effortlessly? We call this PTaaS, powered by SecurePortal.


Find & Fix Vulnerabilities
With PTaaS (Penetration Testing as a Service) you gain the ability to scan for vulnerabilities alongside your regular penetration testing services. Detecting and alerting you of any major risks so you can remediate before they're exploited by an attacker.

Easily Distribute
Remediation
Tasks
PTaaS is powered by SecurePortal and allows you and your team to assign remediation tasks per user account. Rather than spending time and resources analysing a lengthy report you can jump to a specific vulnerability and give control of it to a team member, allowing you to monitor their progress and easily remove vulnerabilities without lengthy procedures.

Talk to an Expert About Your Cyber Security Options
Fill out our contact form and a member of the team will be in touch to discuss your needs and offer support or contact is by phone on 0330 311 0990

Manage The Testing
Process
We developed our Penetration Testing approach by analysing the most challenging aspects that clients encounter. By identifying the biggest
time-consuming steps and negative factors, we explored ways to simplify the entire process.
With PTaaS, we provide a fully digital service that streamlines the approach to Penetration Testing for your team. This leads to an easier process for everyone involved and makes securing your business simple.

Reduce Your Window
of Risk
By taking this approach to your businesses security you're actively reducing your window of risk. Blend automated scanning with consultant led tests and you're monitoring all areas of your organisation for vulnerabilities and misconfigurations.
Get in touch and learn how PTaaS can help your business.

The PTaaS Timeline
Our PTaaS Service Has Three Simple Steps Alongide Ongoing Scanning For The Best in Vulnerability Detection

Get Access To SecurePortal
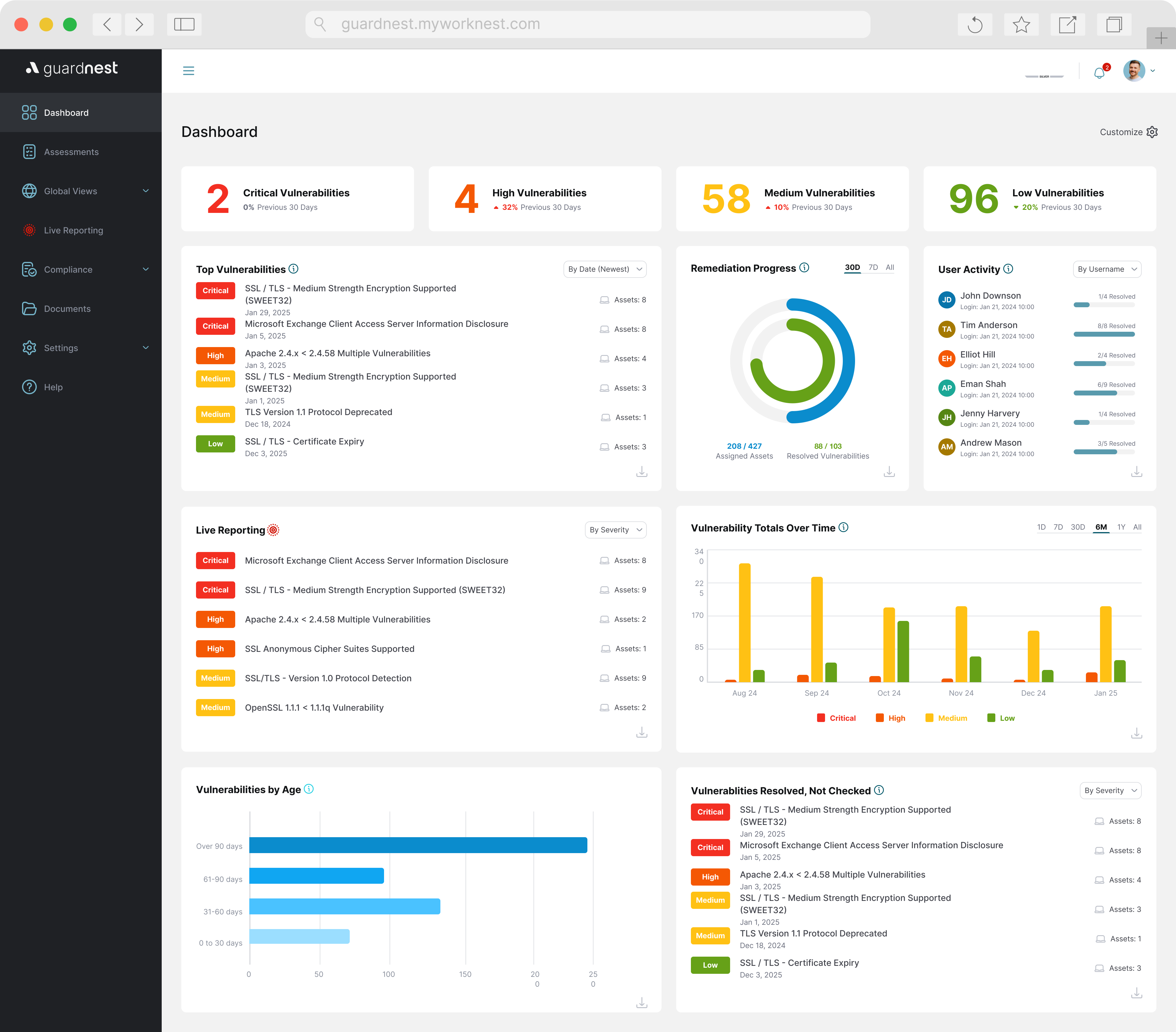
Digitalising Your Penetration Testing with GuardNest
Make Your Testing Experience Easier with a Dynamic Vulnerability Portal
GuardNest provides clients with a new way to monitor and analyse the data you receive in your penetration tests. Rather than a lengthy physical report you gain a range of simple features that highlight your test findings and vulnerabilities.
Easily access remediation advice from our team of consultants on discovered vulnerabilities and assign them to your team for fast and efficient resolution. Receive overview and trend data of all of the current security issues you face in your organisation.
Pentest People Are Trustworthy & Experienced





Benefits of PTaaS
Why Does Your Business Need The PTaaS Model?

Discover Vulnerabilities Effeciently
With automated testing alongside your regular penetration tests you can detect vulnerabilities more efficiently and reduce your risk window.

Manage Remediation More Effectively
Remediation has never been easier. Assign the tasks to your respective team members and monitor their progress.

Digitalised Reports Make Analysis Simple
Navigate through your digital report with ease and jump to the most relevant concerns, such as critical vulnerabilities that require immediate action.
See What Our Clients Have to Say About our Professional Services
Need More Info on Our Infrastructure Testing?
Frequently Asked Questions
Can PTaaS help with compliance requirements?
Yes, PTaaS platforms are designed to help organizations meet various industry compliance standards, such as PCI-DSS, HIPAA, GDPR, and others. Continuous testing ensures that organizations can maintain compliance by regularly identifying and addressing security vulnerabilities.
What are the benefits of PTaaS?
PTaaS offers several benefits, including:
- Continuous Security Management: Ongoing testing allows for the identification and remediation of vulnerabilities as they arise.
- Cost-effectiveness: PTaaS reduces costs compared to traditional in-house penetration testing by leveraging automation and scalable solutions.
- Adherence to Industry Standards: Easier compliance with standards such as SANS and OWASP.
- Real-time Data Access: Immediate access to vulnerability data enables prompt action and remediation.
- Flexibility and Scalability: PTaaS platforms like SecirePortal support various testing types and can scale according to organisational needs
What is Penetration Testing as a Service (PTaaS)?
Penetration Testing as a Service (PTaaS) is a comprehensive cybersecurity service offered by Pentest People, aimed at identifying vulnerabilities and assessing the security of a computer system, network, or software application. PTaaS involves conducting simulated attacks, penetration tests and ongoing scanning in order to proactively identify potential weaknesses and security gaps in order to strengthen the overall security posture. This service provides valuable insights and recommendations for remediation, helping organisations to protect their sensitive data and assets from potential threats.
How does PTaaS differ from a standard Penetration Test?
Traditional penetration testing is typically a point-in-time assessment conducted once or twice a year, resulting in a static report. In contrast, PTaaS offers continuous testing with real-time reporting, allowing for immediate action on identified vulnerabilities. PTaaS integrates more seamlessly with modern development practices, providing ongoing security assessments and reducing the time to remediation
What is PTaaS
Penetration Testing as a Service (PTaaS) is a modern cybersecurity solution that combines automated and manual testing to identify vulnerabilities in an organization's IT infrastructure. PTaaS platforms enable continuous security management, allowing businesses to regularly test, identify, and remediate vulnerabilities in real-time, rather than relying on infrequent, point-in-time assessments.
.png)





















.svg)








.webp)


