Windows IPv6 – Part One


Windows IPv6 – Part One
Hidden Threats From Default IPv6 Configurations
We are all aware of IPv6 but are we aware of the current threats associated with default configurations? What is the new threat landscape with IPv6? Should we turn a blind eye and hope it disappears? I won’t cover every IPv6 detail and attack; only the most relevant at the moment. This Pentest People series will contain a mix of technical and non-technical material so stay tuned for more.
With an Internet of Things (IoT) apocalypse, we are quickly exhausting the IPv4 address pool. We are in need of a more complex network protocol with a greater address pool. Luckily, lPv6 has 340 undecillion possible addresses available. For perspective, we could give every star in the largest galaxy (IC 1101 has 100* trillion stars) an IPv6 address and have more than enough left.
Tl;dr – Attackers can Man-in-the-Middle (MITM) Windows 7+ by sending IPv6 DHCP configurations to become the preferred DNS server.
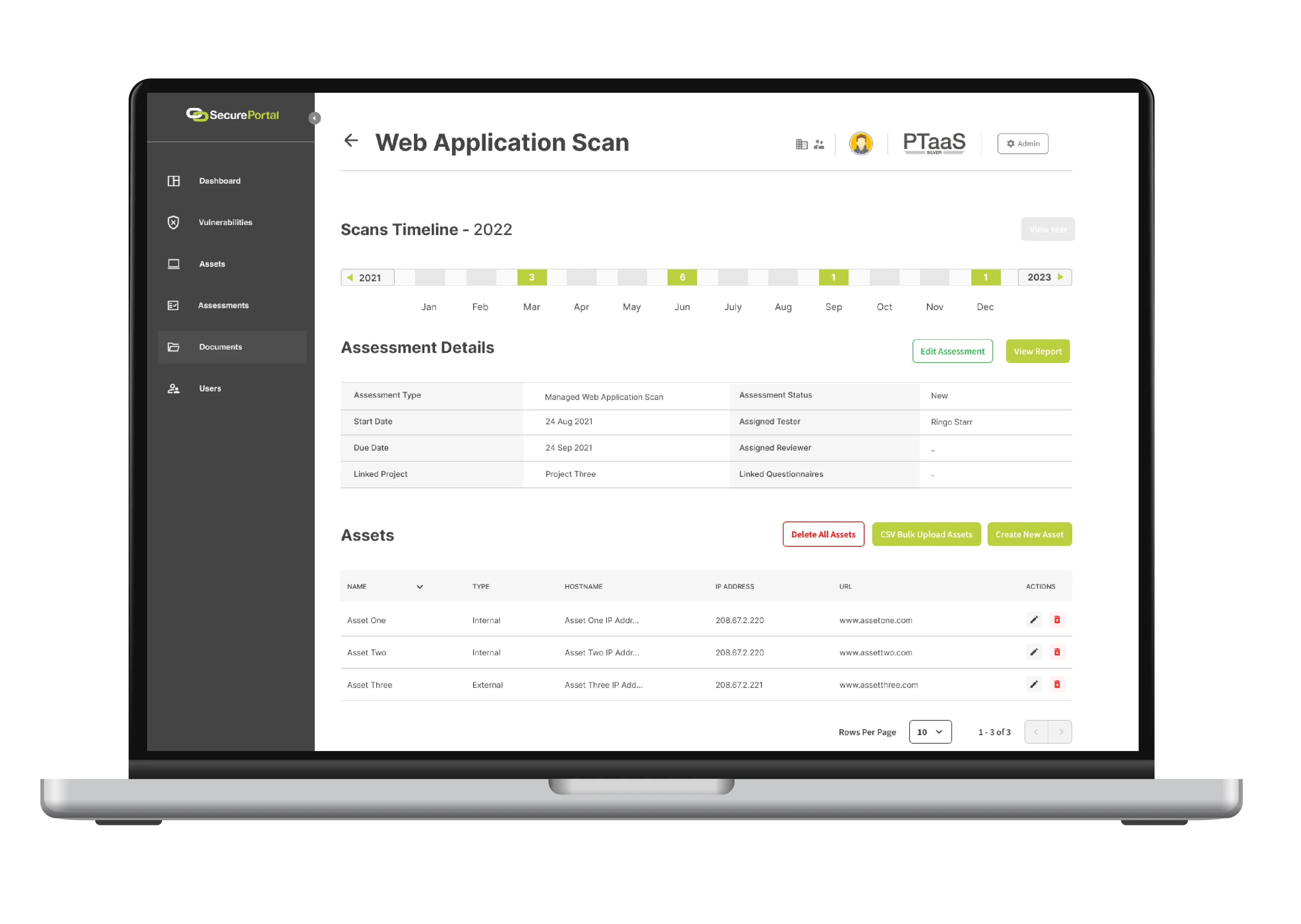
IPv6 in Windows Environments
To clear up any confusion, IPv6 being enabled is not the vulnerability — leaving it as default is. Windows Vista and above (including the Server varieties) have IPv6 enabled and are configured to prefer it over IPv4. This is an issue as the operating system will frequently attempt to find an IPv6 DHCP server to grab configurations from. The DHCPv6 requests can be analysed by running Wireshark with the following filter ‘udp.port == 546 or udp.port == 547’ (546 is for clients and 547 is for servers).
An attacker can abuse Windows’ DHCPv6 requests to become the designated DNS server, and as IPv6 is preferred, all requests will be sent to the attacker. This can be chained in a multitude of ways to compromise the system and potentially the network. The main attack would be capturing credentials (both hashed and cleartext) from protocols such as HTTP, SMBv1/2 and SQL Browser. The only limitation is the attacker’s imagination.

Remediations
There are several ways of combating and managing IPv6 in your IPv4 network. Pentest People recommend thoroughly testing each fix before implementing them into your live environment.
Easiest Route
This is not Microsoft’s preferred method as IPv6 is a “mandatory” part of the OS and disabling it “could” cause issues. However, the easiest way to remediate vulnerabilities is by unplugging the server and burying it. With that school of thought applied, if IPv6 is not on your roadmap and you have no plans of supporting it; disable it. Alternatively, you can disable DHCP on all IPv6 interfaces, however, Microsoft have not commented on this yet. However, this method will not stop all IPv6 attacks.
Microsoft’s Route
This method is fully supported by Microsoft but does not offer full protection against IPv6 attacks without additional security implementations. Instead of disabling IPv6, you implement a registry fix to prefer IPv4 over IPv6.
Secure Route
This option is the most comprehensive and offers the most protection for your networks if IPv6 is on your roadmap. Starting from the wire up, configuring DHCPv6 Guard and Router Advertisement (RA) Guard on network equipment. Implementing a legitimate IPv6 DHCP server to offer IPv6 configurations and modify the registry to prefer IPv4. Lastly, Intrusion Detection Systems (IDS) could be implemented to detect and alert on malicious DHCP servers.
Registry Entry:
Location: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Tcpip6\Parameters\
Name: DisabledComponents
Type: REG_DWORD
Value: 0xFF (IPv6 disabled) or 0x20 (Prefer IPv4 over IPv6)
Powershell Command:
Get-NetIPInterface
Set-NetIPInterface InterfaceAlias -AddressFamily IPv6 -dhcp disabled
External References For IPv6
Find out more about our Web Application Testing Services here or for any of our other services, check out our service pages.



.webp)






.svg)







.webp)

